On-premise authentication
Overview
To deliver authentication, Data Hub supports various authentication providers. By default, the Windows authentication provider is used. The product ships with two other providers: ADFS and Microsoft Entra ID (formerly AzureAD), both of which use claims-based authentication.
Providers:
Active Directory (Windows) - Default Data Hub is configured to use Windows authentication; no additional configuration is required. Windows authentication recognizes local system users and groups configured on the webserver computer, as well as Active Directory users and groups configured for the web server's domain.
Microsoft Entra ID - (formerly Azure Active Directory (Azure AD)) – Entra ID allows claims-based user and group management for Data Hub and other on-premises and cloud applications, such as Office 365 and Dynamics CRM Online. Once configured, users logging into Data Hub will be redirected to Microsoft Entra ID to authenticate.
Active Directory Federation Services (ADFS) - ADFS implements claims-based federated identity for Windows for Data Hub installations. ADFS enables single sign-on to authenticate users across security and enterprise boundaries.
Okta -
OpenID Connect -
 |
Configure application authentication settings
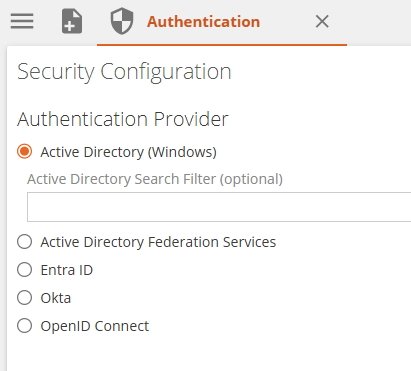
Select your application authentication method using the Authentication area of the Settings tab.
 |
Windows (Active Directory) authentication – allows you to authenticate users within an Active Directory domain.
Entra ID authentication – allows claims-based authentication using Microsoft Entra ID.
Active Directory Federation Services (ADFS / WSFederation) authentication – allows claims-based authentication using Microsoft ADFS.
Allow Anonymous Viewers check box – When selected, allows any unauthenticated users to view links that have been shared with them.
Note
The Allow Anonymous Viewers feature may require a specific license permission to use. Without permission, the check box may not be visible.
Only resources in the Public folder (and its subfolders) may be shared with this feature.
To share a resource or folder with anonymous viewers, its viewer access setting must be enabled, by displaying the resource's security screen, and then clicking the Viewer Access on the HOME screen.
You may also need to override the inheritance of security permissions for the resource (Override on the security screen's HOME screen) before you can enable Viewer Access.
Windows (Active Directory) authentication
Windows (Active Directory) requires no further configuration. Data Hub uses the application pool identity of the webserver it is installed on to access Active Directory to authenticate users. Local system users and groups configured on the webserver computer, as well as Active Directory users and groups configured for the web server's domain may be used.
The best practice for Active Directory authentication is to use the AGDLP nested group model to minimize administration.
Note
Users from other domains may also authenticate if the appropriate trusts and group structures are set up.
The optional Active Directory Search Filter box lets you type an LDIF string to specify the distinguished name (DN) of the organization unit (OU) to use for Active Directory searches.
For example, to specify the US\Washington OU for the contoso.com domain, type: OU=Washington, OU=US, DC=contoso, DC=com.
Specifying a search filter may be useful if you have many users in your Active Directory, or your Active Directory is distributed across multiple sites connected by WAN links, in order to improve performance. Any filter specified here will be applied when you search for users and groups to add to a Data Hub policy in the Users and Groups screen.
 |
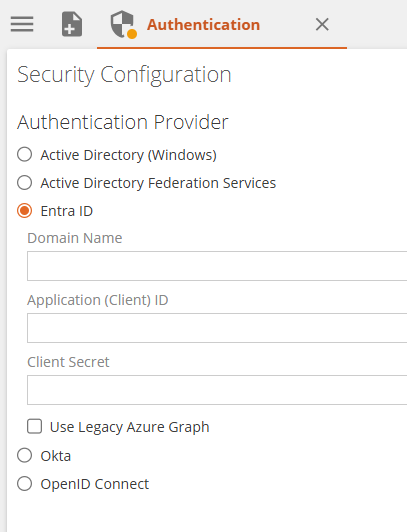
Microsoft Entra ID (formerly Active Directory (AzureAD)) authentication
Entra ID allows claims-based user and group management for Data Hub and other on-premises and cloud applications, such as Office 365 and Dynamics CRM Online. Once configured, users logging into Data Hub will be redirected to Microsoft Entra ID to authenticate.
To use Data Hub with Entra ID:
Complete an application registration for Data Hub in the Azure portal to obtain the Tenant(Domain Name), Client ID and Client Secret values. Instructions can be found in the following Knowledge Base article: https://zendesk.zaptechnology.com/hc/en-us/articles/207150197.
Provide Tenant, Client ID, and client secret values retrieved from the registration process here.
 |
Use Active Directory Federation Services (ADFS) authentication
ADFS implements claims-based federated identity for Windows for your Data Hub installation. ADFS enables single sign-on to authenticate users across security and enterprise boundaries.
To use Data Hub with ADFS:
Configure a relying party trust in the ADFS Management console, and the Federation Metadata URL and enter Realm URI (the Data Hub application's web address) into the appropriate boxes in the Configure Security Settings screen.
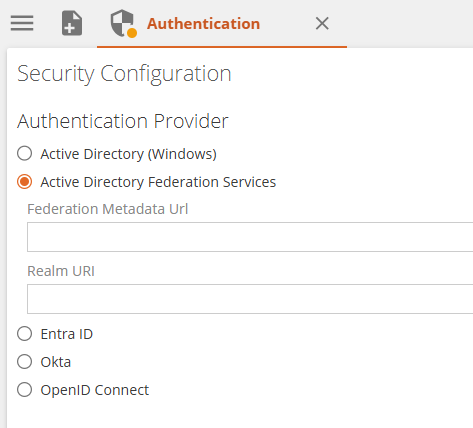 |
For details on configuring a relying party trust and obtaining the Federation Metadata URL and Realm URI values, values, refer to the following Knowledge Base article:
Okta
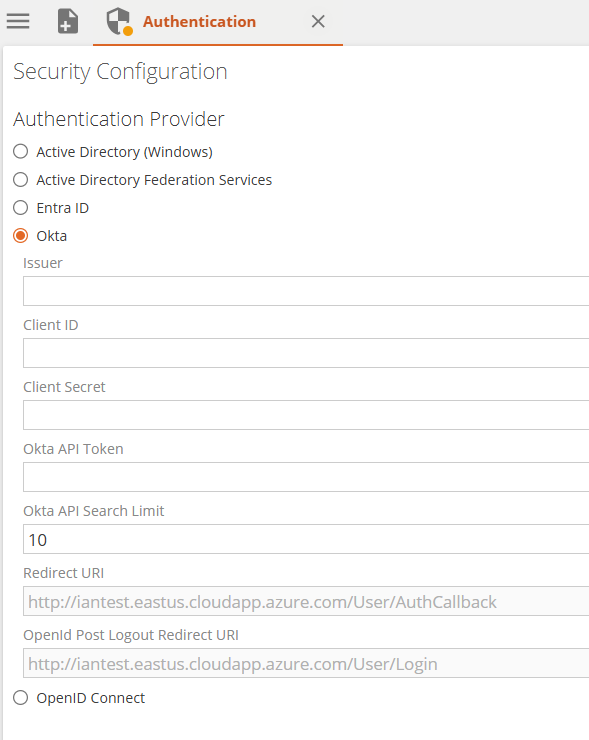 |
Open ID
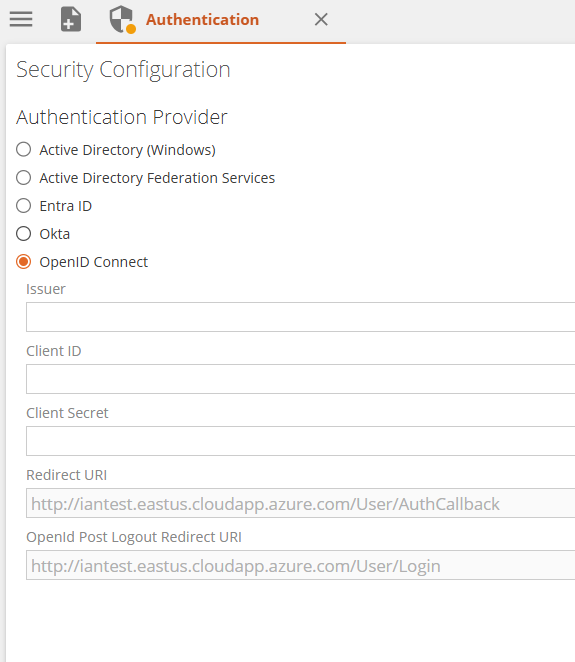 |
Refresh user and group Information
If you are using Active Directory or Active Directory Federation Services (ADFS), you can manually force Data Hub to update the information displayed on the Users and Groups tab by clicking Clear Membership Cache on the HOME screen.
This action allows you to guarantee that you are viewing the most up-to-date user and group information.
If you do not want to wait for the database to automatically update new users or groups in Active Directory, you can force Data Hub to contact Active Directory and perform an IIS refresh to retrieve the new user or group information.